How secure is Windows Remote Desktop?
- Microsoft Authenticator App Download For Pc
- Outlook And Microsoft Authenticator
- Microsoft Authenticator Rdp App
The next page defines the authentication requirements. For this scenario select Request authentication for inboard and outbound connections. With that option the devices which share this connection agreement will attempt to negotiate IPsec but if the negotiation fails, the devices will continue to communicate. The Microsoft Authenticator app also supports the industry standard for time-based, one-time passcodes (also known as TOTP or OTP). Because of that, you can add any online account that also supports this standard to the Microsoft Authenticator app. This will help keep your other online accounts secure.
Remote Desktop sessions operate over an encrypted channel, preventing anyone from viewing your session by listening on the network. However, there is a vulnerability in the method used to encrypt sessions in earlier versions of RDP. This vulnerability can allow unauthorized access to your session using a man-in-the-middle attack.
Remote Desktop can be secured using SSL/TLS in Windows Vista, Windows 7, Windows 8, Windows 10 and Windows Server 2003/2008/2012/2016. *Some systems listed are no longer supported by Microsoft and therefore do not meet Campus security standards. If unsupported systems are still in use, a security exception is required.
While Remote Desktop is more secure than remote administration tools such as VNC that do not encrypt the entire session, any time Administrator access to a system is granted remotely there are risks. The following tips will help to secure Remote Desktop access to both desktops and servers that you support.
Basic Security Tips for Remote Desktop
1. Use strong passwords
Strong passwords on any accounts with access to Remote Desktop should be considered a required step before enabling Remote Desktop. Refer to the campus password complexity guidelines for tips.
2. Use Two-factor authentication
Departments should consider using a two-factor authentication approach. This topic is beyond the scope of this article, but RD Gateways can be configured to integrate with the Campus instance of DUO. Other unsupported by campus options available would be a simple mechanism for controlling authentication via two-factor certificate based smartcards. This approach utilizes the Remote Desktop host itself, in conjunction with YubiKey and RSA as examples.
3. Update your software
Microsoft Authenticator App Download For Pc
One advantage of using Remote Desktop rather than 3rd party remote admin tools is that components are updated automatically with the latest security fixes in the standard Microsoft patch cycle. Make sure you are running the latest versions of both the client and server software by enabling and auditing automatic Microsoft Updates. If you are using Remote Desktop clients on other platforms, make sure they are still supported and that you have the latest versions. Older versions may not support high encryption and may have other security flaws.
4. Restrict access using firewalls
Use firewalls (both software and hardware where available) to restrict access to remote desktop listening ports (default is TCP 3389). Using an RDP Gateway is highly recommended for restricting RDP access to desktops and servers (see discussion below). As an alternative to support off-campus connectivity, you can use the campus VPN software to get a campus IP address and add the campus VPN network address pool to your RDP firewall exception rule. Visit our page for more information on the campus VPN service.
5. Enable Network Level Authentication
Windows 10, Windows Server 2012 R2/2016/2019 also provide Network Level Authentication (NLA) by default. It is best to leave this in place, as NLA provides an extra level of authentication before a connection is established. You should only configure Remote Desktop servers to allow connections without NLA if you use Remote Desktop clients on other platforms that don't support it.
NLA should be enabled by default onWindows 10, Windows Server 2012 R2/2016/2019.
To check you may look at Group Policy setting Require user authentication for remote connections by using Network Level Authentication found at ComputerPoliciesWindows ComponentsRemote Desktop ServicesRemote Desktop Session HostSecurity. This Group Policy setting must be enabled on the server running the Remote Desktop Session Host role.
6. Limit users who can log in using Remote Desktop
By default, all Administrators can log in to Remote Desktop. If you have multiple Administrator accounts on your computer, you should limit remote access only to those accounts that need it. If Remote Desktop is not used for system administration, remove all administrative access via RDP, and only allow user accounts requiring RDP service. For Departments that manage many machines remotely remove the local Administrator account from RDP access at and add a technical group instead.
Click Start-->Programs-->Administrative Tools-->Local Security Policy
Under Local Policies-->User Rights Assignment, go to 'Allow logon through Terminal Services.' Or “Allow logon through Remote Desktop Services”
Remove the Administrators group and leave the Remote Desktop Users group.
Use the System control panel to add users to the Remote Desktop Users group.
A typical MS operating system will have the following setting by default as seen in the Local Security Policy:
The problem is that “Administrators” is here by default, and your “Local Admin” account is in administrators. Although a password convention to avoid identical local admin passwords on the local machine and tightly controlling access to these passwords or conventions is recommended, using a local admin account to work on a machine remotely does not properly log and identify the user using the system. It is best to override the local security policy with a Group Policy Setting.
To control access to the systems, even more, using “Restricted Groups” via Group Policy is also helpful.
If you use a “Restricted Group” setting to place your group, e.g., “CAMPUSLAW-TECHIES” into “Administrators” and “Remote Desktop Users,” your techies will still have administrative access remotely, but using the steps above, you have removed the problematic “local administrator account” having RDP access. Going forward, whenever new machines are added in the OU under the GPO, your settings will be correct.
7. Set an account lockout policy
By setting your computer to lock an account for a set number of incorrect guesses, you will help prevent hackers from using automated password guessing tools from gaining access to your system (this is known as a 'brute-force' attack). To set an account lockout policy:
- Go to Start-->Programs--> Administrative Tools--> Local Security Policy
- Under Account Policies--> Account Lockout Policies, set values for all three options. Three invalid attempts with 3-minute lockout durations are reasonable choices.
Best Practices for Additional Security

1. Do not allow direct RDP access to clients or servers from off campus.
Having RDP (port 3389) open to off campus networks is highly discouraged and is a known vector for many attacks. The options below list ways of improving security while still allowing RDP access to system.
Once an RDP gateway has been set up, hosts should be configured to only allow RDP connections from the Gateway host or campus subnets where needed.
2. Use RDP Gateways (Best Option)
Using an RDP Gateway is strongly recommended. It provides a way to tightly restrict access to Remote Desktop ports while supporting remote connections through a single 'Gateway' server. When using an RD Gateway server, all Remote Desktop services on your desktop and workstations should be restricted to only allow access only from the RD Gateway. The RD Gateway server listens for Remote Desktop requests over HTTPS (port 443) and connects the client to the Remote Desktop service on the target machine.
Utilize Campus RDP Gateway Service. This is the best option to allow RDP access to system categorized as UC P2 and lower. Includes DUO integration. RDP Gateway Service is provided by the Windows Team. Documentation is available here: https://berkeley.sharepoint.com/sites/calnetad/gateway.
The RDP Gateway Service also supports the new Remote Access Services requirement of the draft MSSND update (requirement 8), which requires the use of an approved service (i.e., RDP gateway, dedicated gateway, or bSecure VPN) for access to the UC Berkeley network from the public Internet.
Dedicated Gateway Service (Managed). Needed for rdp access to systems that are UC P4 or higher. Must also be configured for DUO
Some campus units use an IST managed VPS as an RD Gateway. A rough estimate might be that 30-100 concurrent users can use one RD Gateway. The HA at the virtual layer provides enough fault-tolerant and reliable access; however a slightly more sophisticated RD gateway implementation can be done with network load balancing.- Dedicated Gateway Service (Unmanaged). Installing and configuring RD Gateway on department run hardware.
There are many online documents for configuring this embedded Windows 2016/2019 component. The official documentation is here: https://docs.microsoft.com/en-us/windows-server/remote/remote-desktop-se...
Installing the configuring, the role service is mostly as described; however, using a Calnet issued trusted Comodo certificate is recommended. Using a self-signed cert is ok for testing, and using a CalnetPKI cert can work if all clients have trusted the UCB root. The Comodo cert is usually better accepted so that your end users do not receive certificate warnings.
Configuring your client to use your RD Gateway is simple.The official documentation for the MS Client is here: http://technet.microsoft.com/en-us/library/cc770601.aspx
In essence, a simple change on the advanced tab of your RDP client is all that is necessary:
3. Change the listening port for Remote Desktop
Changing the listening port will help to 'hide' Remote Desktop from hackers who are scanning the network for computers listening on the default Remote Desktop port (TCP 3389). This offers effective protection against the latest RDP worms such, as Morto. To do this, edit the following registry key (WARNING: do not try this unless you are familiar with the Windows Registry and TCP/IP): HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlTerminal ServerWinStationsRDP-Tcp. Change the listening port from 3389 to something else and remember to update any firewall rules with the new port. Although this approach is helpful, it is security by obscurity, which is not the most reliable security approach. You should ensure that you are also using other methods to tighten down access as described in this article.

4. Tunnel Remote Desktop connections through IPSec or SSH
If using an RD Gateway is not feasible, you can add an extra layer of authentication and encryption by tunneling your Remote Desktop sessions through IPSec or SSH. IPSec is built-in to all Windows operating systems since Windows 2000, but use and management are greatly improved in Windows 10 (see: http://technet.microsoft.com/en-us/network/bb531150). If an SSH server is available, you can use SSH tunneling for Remote Desktop connections.
5. Use existing management tools for RDP logging and configuration
Using other components like VNC or PCAnywhere is not recommended because they may not log in a fashion that is auditable or protected. With RDP, logins are audited to the local security log, and often to the domain controller auditing system. When monitoring local security logs, look for anomalies in RDP sessions such as login attempts from the local Administrator account. RDP also has the benefit of a central management approach via GPO as described above. Whenever possible, use GPOs or other Windows configuration management tools to ensure a consistent and secure RDP configuration across all your servers and desktops.
By enforcing the use of an RDP gateway, you also get a third level of auditing that is easier to read than combing through the domain controller logins and is separate from the target machine so it is not subject to tampering. This type of log can make it much easier to monitor how and when RDP is being used across all the devices in your environment.
This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.
Need a quick and easy 2FA setup for Windows and RDP logons? This might help…
So I recently had a challenge where I needed to add 2FA (specifically, using the Microsoft Authenticator service) to a Windows 10 logon for a particular set of users. Rather naively, I assumed that you would be able to do this simply using the Microsoft Authenticator service directly, but I was surprised to find that this functionality wasn’t offered. The way Microsoft recommend to do it was by using Windows Hello, but within a few minutes of reading the literature around it, it was clear that there was a *lot* of work required to get Windows Hello up and running – and it wasn’t exactly fully foolproof either.
There’s alot of requests to extend the Microsoft Authenticator service onto Windowsconsole logons and RDP logons, and since MS have sunset the on-premises MFAserver this is only increasing. Microsoft seem hell-bent on pushing through thepasswordless, biometric concept of Windows Hello, and while this is somethingthat no doubt will gain much traction in the future, legacy systems withpasswords and MFA aren’t going away anytime soon. So, in the absence ofAuthenticator being integrated with Windows 10, it started to look like I wason the hunt for a (preferably free or low-cost!) third-party provider.
Duo are one of the leaders in this category, but given that their freeversion only extends to ten users, it didn’t fit my needs. Enter Leee Jeffriesto tell me about ManageEngine’s AD Self Service Plus product, which is free forup to fifty users (and, if I’m not mistaken, seems to be owned by Zoho). Thislooked really promising, so off I set to see how easy it was to get up andrunning.
Installing the software
First I set out to install my AD SelfService Plus software
The default port for the web service is 8888 – if you wish to use a different port, you can enter it at this point
The installation will then proceed
Once the installation is finished, you can launch the console from the desktop shortcut, and you can also install it as a Windows service if you wish (from the Start menu shortcuts)
If you doinstall the software as a service, the server will need to be rebooted beforeit activates. Also, it is recommended to run the service as a domain accountrather than LocalSystem, especially if it is going to be doing remotedeployments of the client software from the console.
As theconsole runs in a browser, you may need to turn off IE Enhanced SecurityConfiguration if you are intending to access it from the server desktop.
Setting up SSL
The ADSelfService Plus software uses a Tomcat instance so in order for it to workproperly, you will need to install an SSL certificate.
There are anumber of articles on the ManageEngine site about configuring certificates,however in order to install a self-signed certificate from my own CA I had tofollow this process.
Log on to the console as admin (the default password is also admin)
Go to Admin| Product Settings | Connection
Check “Enable SSL port” and click Save
You canchange the default port from 9251 if you wish. After doing this, restart the ADSelfService Plus service.
Log back into the console as admin again (this time you will probably get a securitywarning, as the certificate was not issued by a trusted CA)
Return toAdmin | Product Settings | Connection.
Click SSL Certification Tool button.
Fill in the required fields for generating the Certificate Signing Request (CSR)
This willgenerate two files – a file called SelfService.csr at webappsadsspCertificatesand a file called SelfService.keystore at jrebin (both paths relativeto the software install directory).
Log on toyour Certificate Authority (https://servername/certsrv) and submit the CSR
Request aCertificate | Advanced Certificate request | Submit a certificate request byusing a base-64-encoded CMC or PKCS #10 file, or submit a renewal request byusing a base-64-encoded PKCS #7 file.
Copy thecontents of the SelfService.csr file into the Saved Request box
Select Web Server from the options for Certificate Template
Click Submitand then click Yes
ClickDownload Certificate to download the certificate in .cer format
ClickDownload Certificate Chain to download the certificate in .p7b format
Place both the files at jrebin
Open an elevatedcommand prompt
Changedirectory to jrebin
Run thefollowing commands
keytool-import -alias tomcat -trustcacerts -file certnew.p7b -keystoreselfservice.keystore
(password isthe password you specified when generating the CSR)
Type ‘y’ or‘Yes’ afterwards and press Enter
.keytool-importkeystore -srckeystore selfservice.keystore -destkeystoreselfservice.keystore -deststoretype pkcs12
(password isthe password you specified when generating the CSR)
keytool-import -alias tomcat -keystore ..libsecuritycacerts -file certnew.cer
(password ischangeit)
Type ‘y’ or‘Yes’ afterwards and press Enter
Copy the SelfService.Keystorefile from jrebin to conf
Back up theserver.xml file
Editserver.xml (you may need to run Notepad elevated to do this)
Replace bothinstances of keystoreFile value with ./conf/SelfService.keystore
Replace bothinstances of keystorePass value with the password you specified whengenerating the CSR
Delete theproperty keystoreType=”PKCS12″
Restart theAD SelfService Plus service
Log back on to the console. You should now see that your SSL certificate is trusted
Firewall configuration
Set up a Windows Firewall rule to allow inbound traffic on TCP port 9251
Configuring the policy
Next we needto configure a policy for our endpoint MFA
Log on tothe console
Click onConfiguration | Policy Configuration
You caneither create a new policy or edit the default one (which will be named afterthe domain)
Select the OUs or Groups that the policy will apply to by clicking the Select OUs/Groups button. I have chosen to apply the policy to an AD group
Click onSave Policy
Switch tothe Multi-factor Authentication submenu on the left
Select thepolicy from the drop-down list and configure your authentication method (we arechoosing Microsoft Authenticator)
Click on Enable Microsoft Authenticator
Switch tothe Authenticator Settings tab
Choose thepolicy you are working on
Enable Endpoint MFA and select the second authentication type. Also, select whether you want users to be enable to log in without 2FA if the AD SelfService Plus system is down
Next, click on Access URL and make sure you have switched to HTTPS with the right port number (9251 by default). It is imperative that this change is made before software is deployed to any target endpoints otherwise it will continue to try and connect on the old port.
Click onSave and then Save Settings
Deploy the client software to endpoints
Next we needto install the client software on the target endpoints where we wish to enableMFA. Whilst this software has an MSI download available which you can use topush the software via SCCM or a similar tool, with the free version, you mustdo the deployment via the console itself.
The endpointrequires two pre-requisites before deployment:-
- Enable the Remote Registry service (either locally or via GPO)
2. Ensure that the target machine can be contacted via Windows File and Print Sharing exception in Windows Firewall (this can be done either locally or via a GPO), as the deployment process connects via the admin$ share
Open the console
Click onConfiguration | Administrative Tools | GINA/Mac/Linux (Ctrl-Alt-Del)
Click onGINA/Mac/Linux installation
In New Installation, locate the target machines you wish to deploy the software to
ClickInstall
Once the install is successful, the console will report success. Checking the target endpoint’s logon screen will now show an additional option as below
Clicking on the new option should successfully show the AD SelfService Plus options as configured in your password policy. If it fails, then remediate the error and try again (certificate issues should present themselves at this point, along with any other communications problems). The below image is similar to what you should see if it is successful (dependent on how the policy is configured)
Enrolling users
Outlook And Microsoft Authenticator
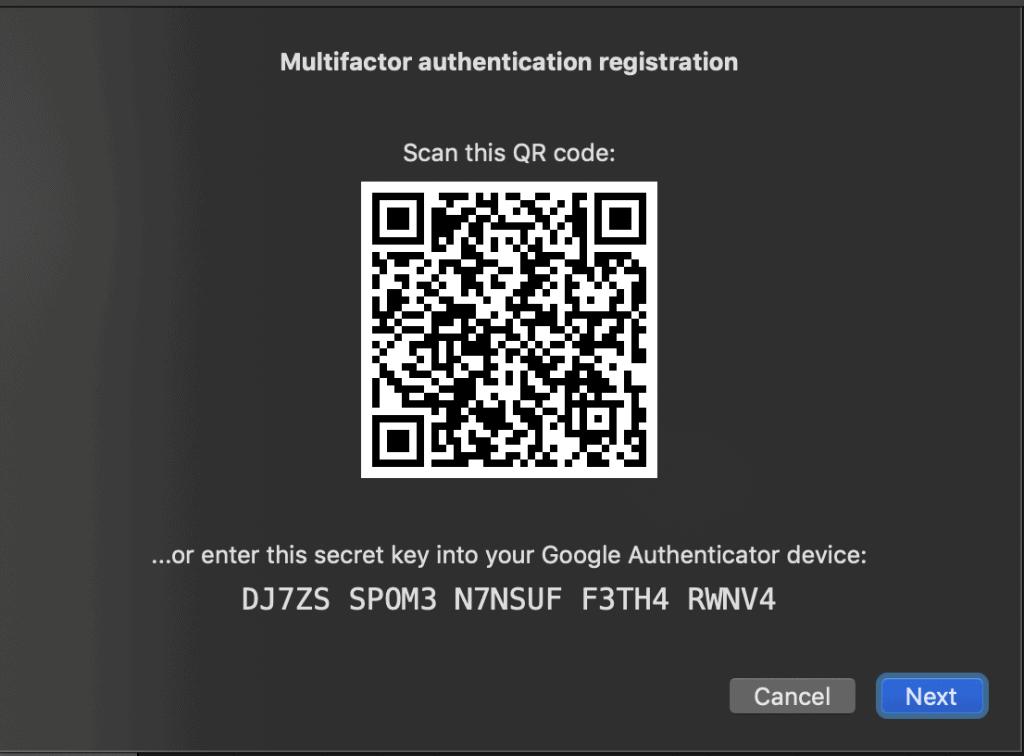
Next you need to enrol the users so that they are set up for the second factor authentication (Microsoft Authenticator in this case). There are various methods within the console that you can force enrolment. For purposes of this demo we are simply going to log the user in to the AD SelfService Plus console where they will be prompted to enrol.
Once the user enters the PIN after they have scanned the QR code, they will be successfully enrolled.
Verifying
Now it’ssimply a case of logging on as the enrolled user and using the MicrosoftAuthenticator app for a second level of verification.
When the user logs on, they should be presented with this screen
They then have to provide the PIN code from Microsoft Authenticator before they can successfully log on. Congratulations, you now have 2FA configured for your Windows network logons (and free for up to 50 users).
Microsoft Authenticator Rdp App
Summary
Obviously if you’re in the Citrix world then there are already a bunch of options available for MFA that are very closely integrated, so this would probably only be on your radar if you needed the free version. For non-Citrix customers though, this could be very useful, particularly for limited-scope deployments like I was looking at.
There is also a huge amount of other functionality available within the AD SelfService Plus software that may prove invaluable from both a security and management perspective, so further exploring the possibilities may well be very fruitful.
38,130 total views, 30 views today
